Install Swavan SSH Studio, complete first launch, and set up your secure vault. Your credentials are encrypted locally — nothing leaves your device.
Visit the GitHub Releases page and download the build for your platform.
- macOS: .dmg universal binary (Apple Silicon + Intel)
- Windows: .msi or .exe installer
- Linux: .AppImage (no install required — see Installation section for FUSE setup)
- iOS / Android: Available via the App Store and Google Play
On first launch you will see the vault setup screen. Three options are available:
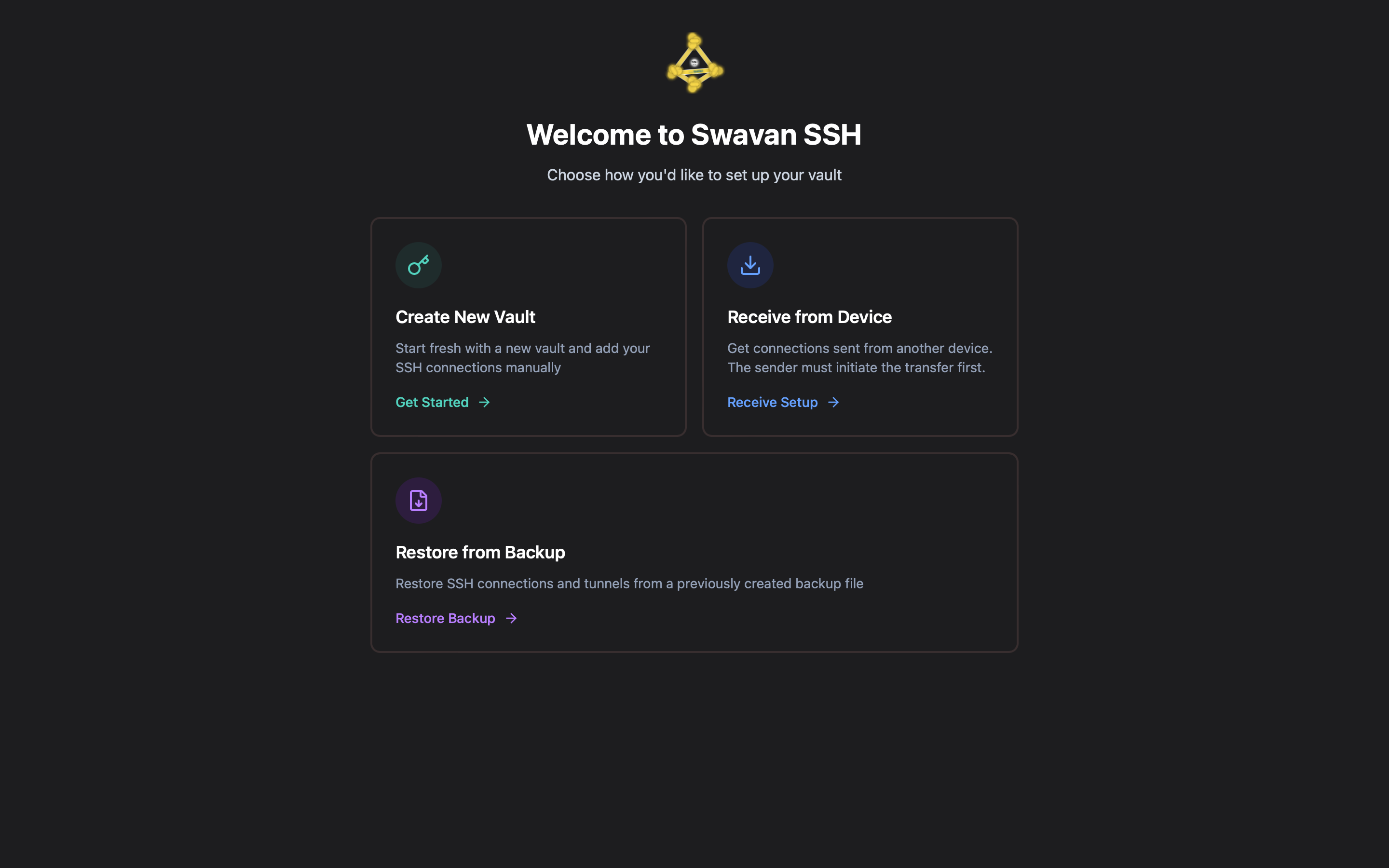
- Create New Vault — start fresh and add connections manually
- Receive from another device — encrypted P2P transfer from an existing device
- Restore from backup — restore from a previously exported encrypted backup file
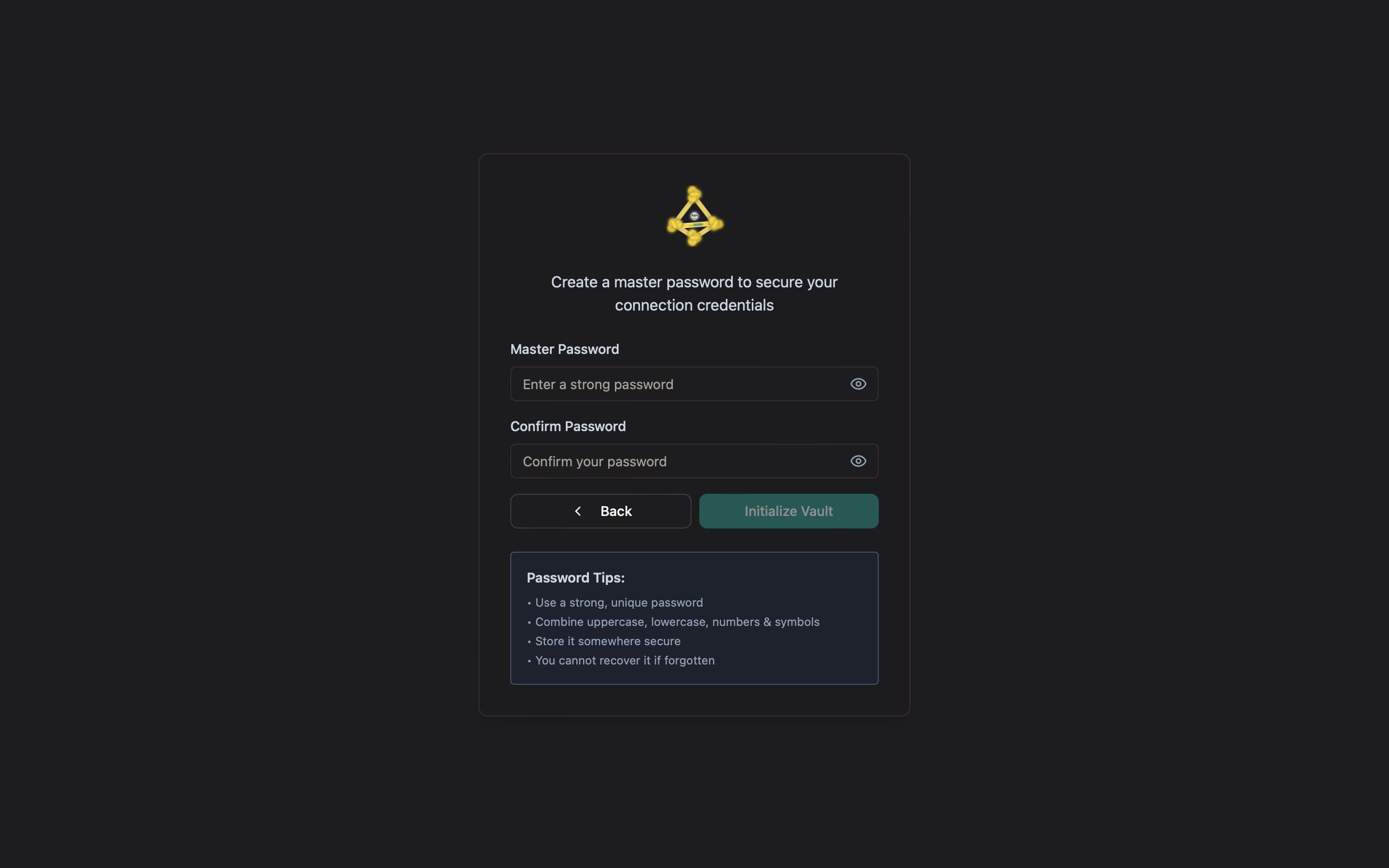
Choose "Create New Vault", enter a strong master password, confirm it, then click Initialize Vault.
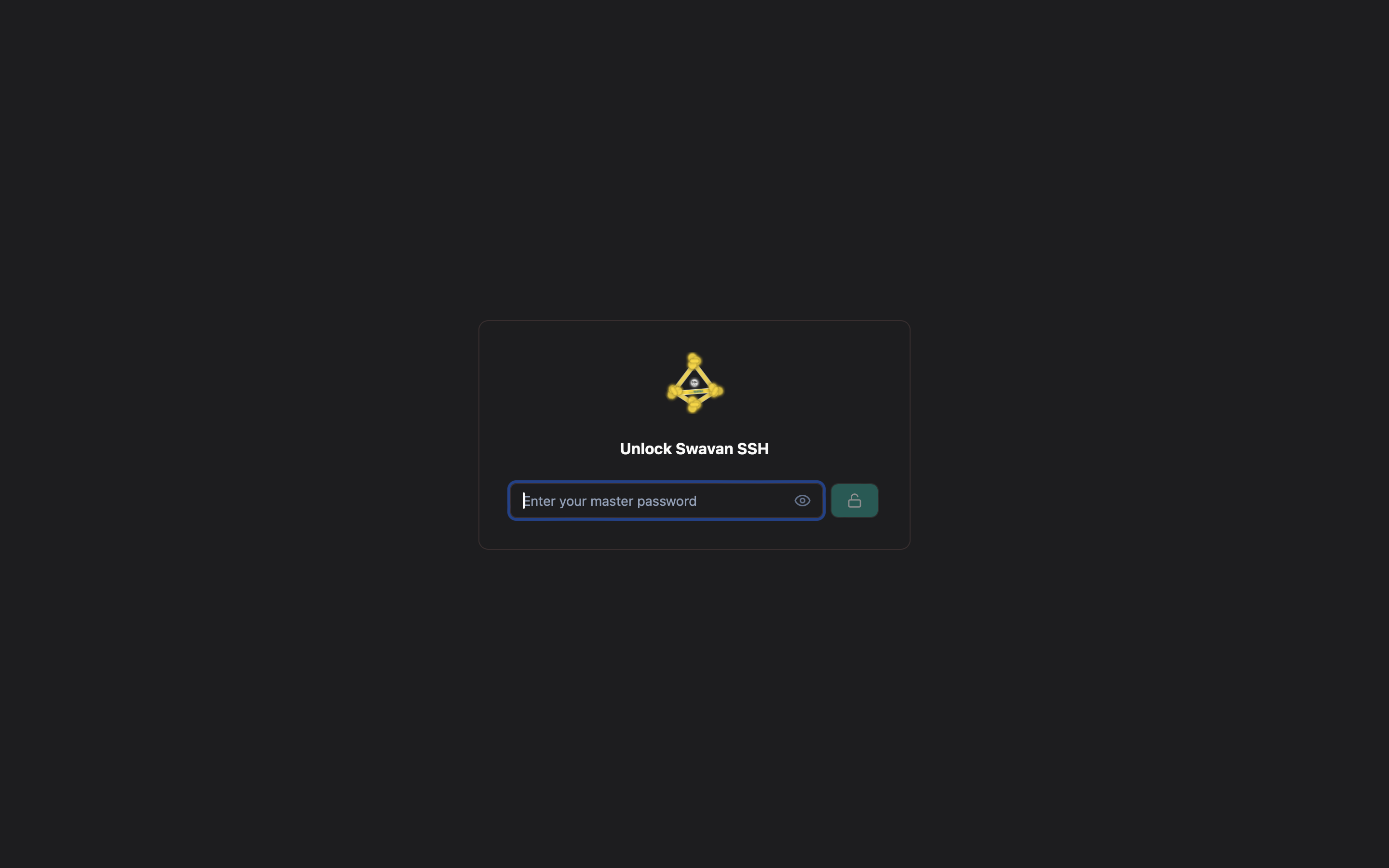
Every time you open the app, enter your master password to unlock the vault.
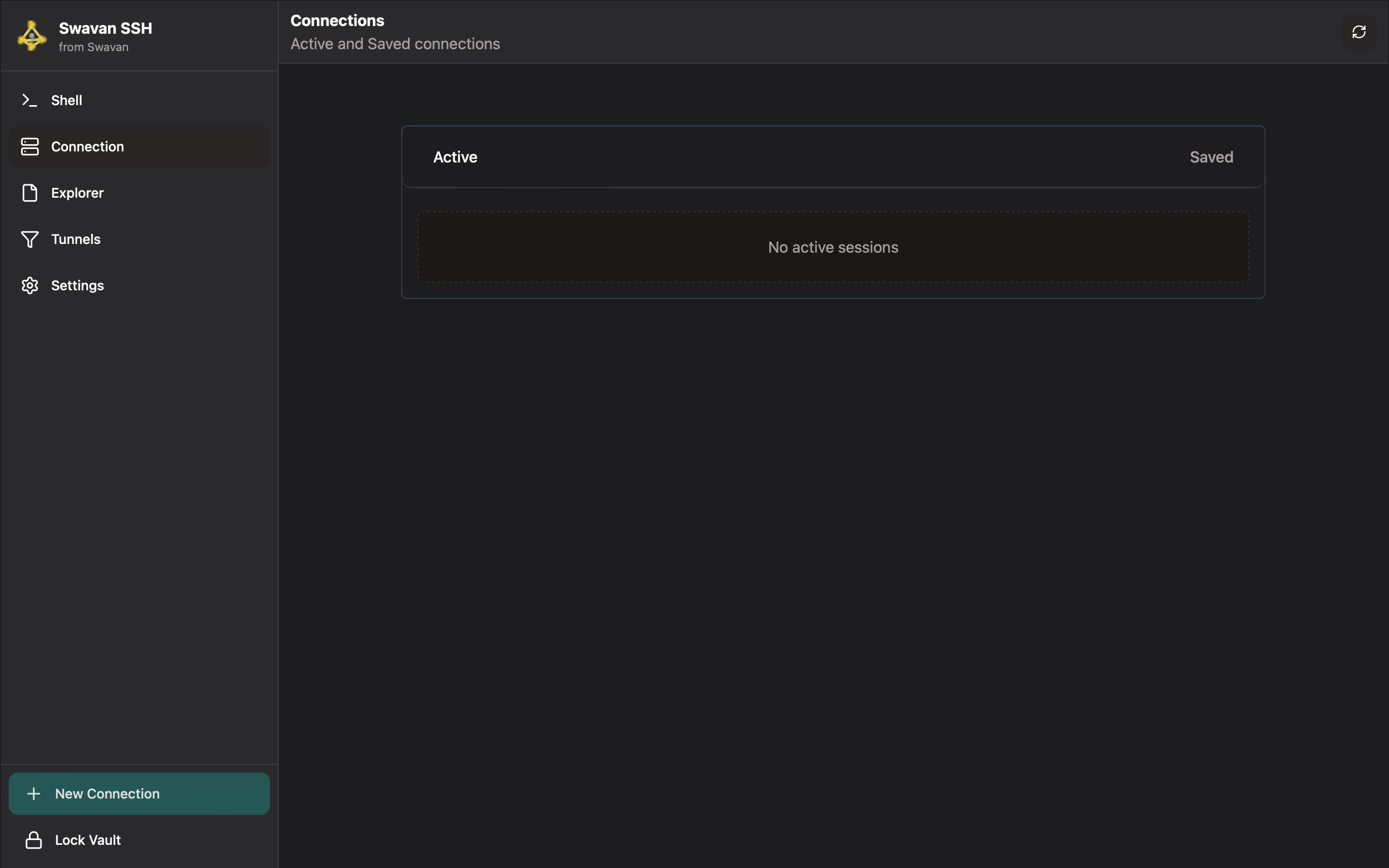
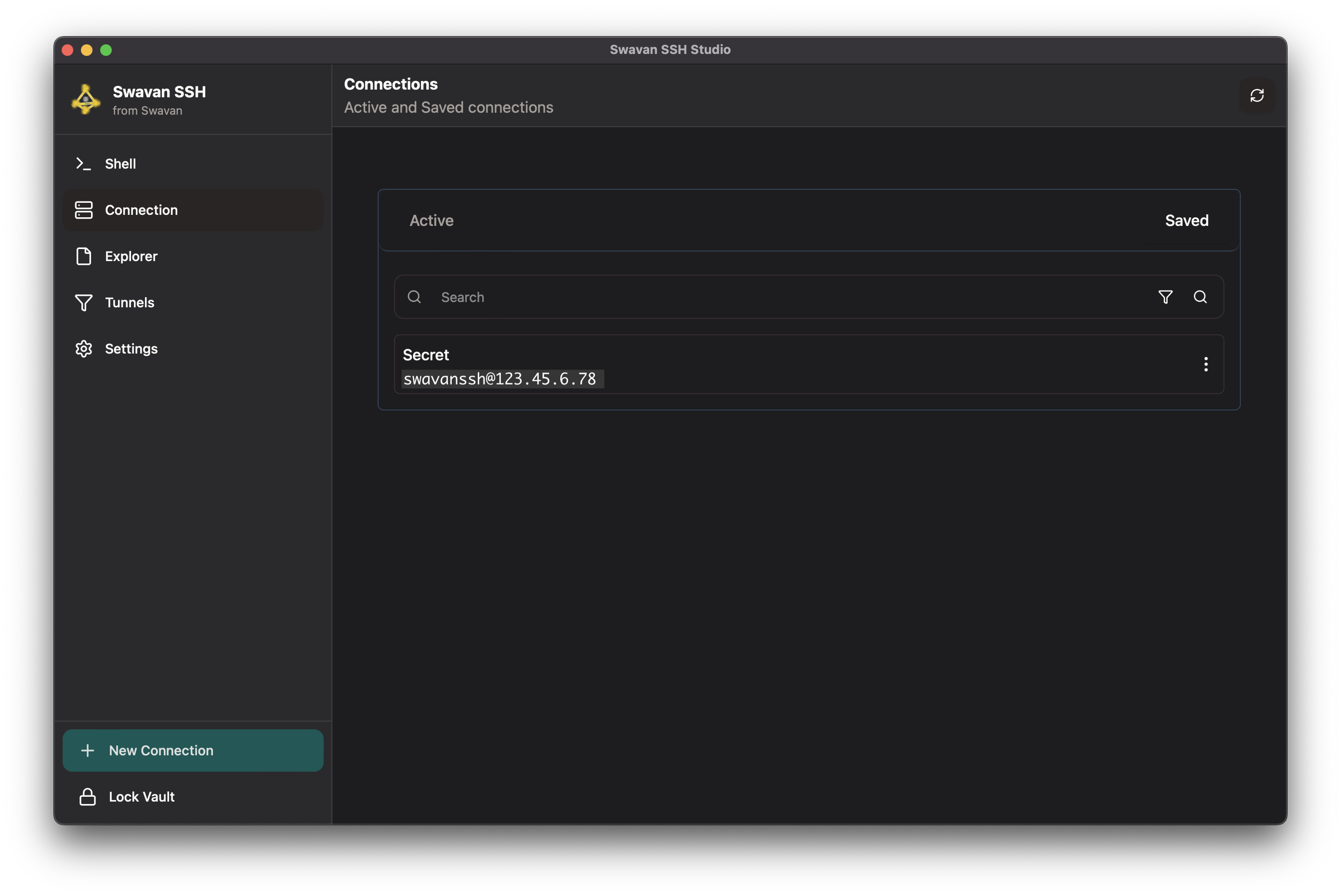
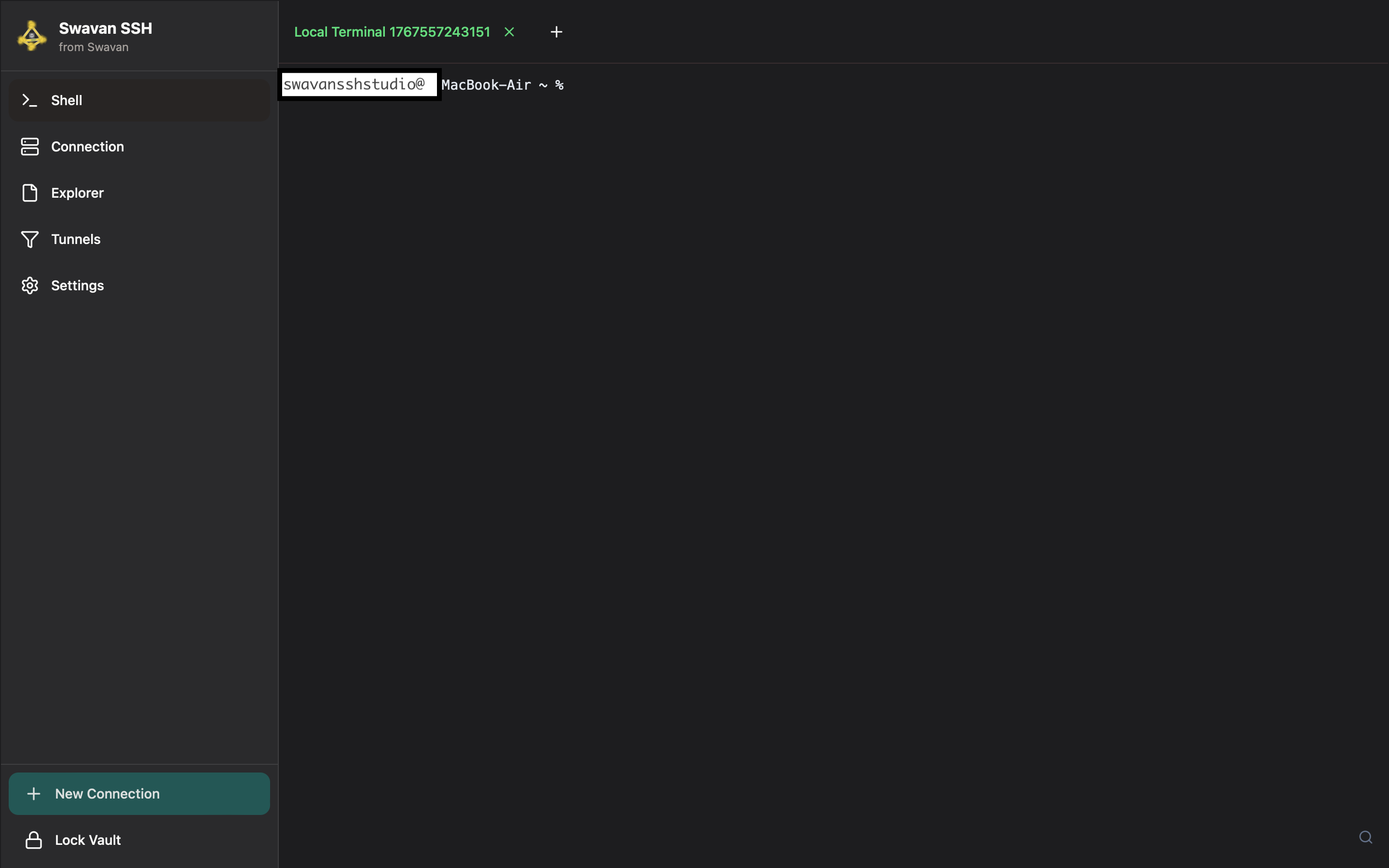
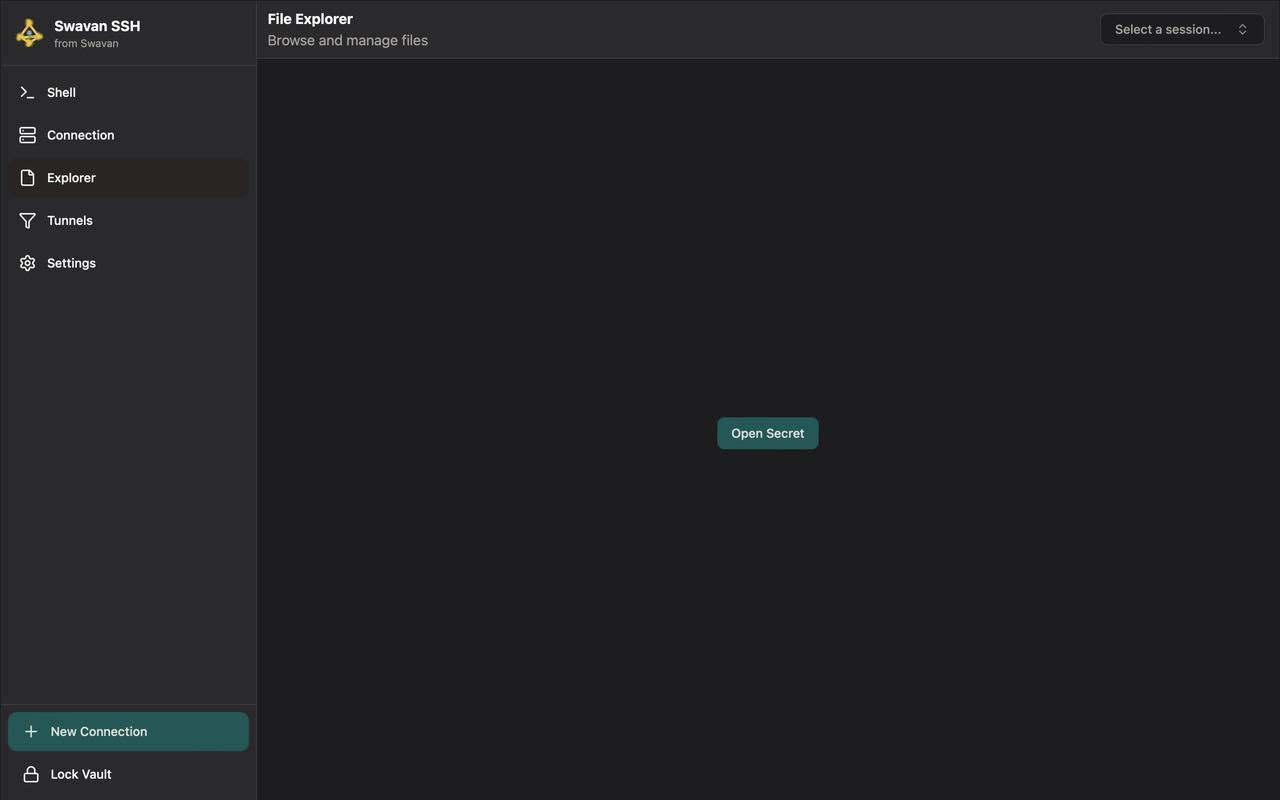
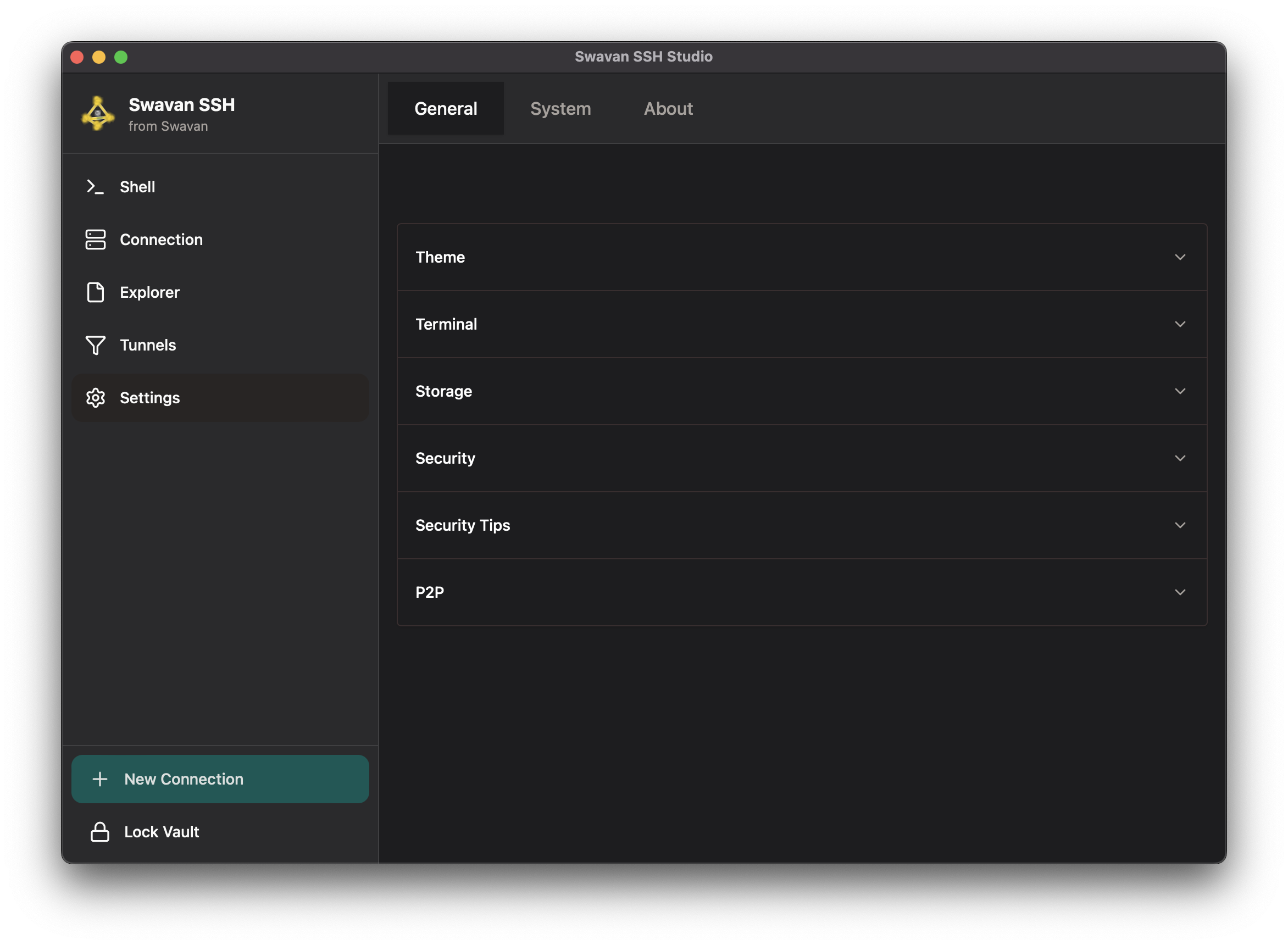
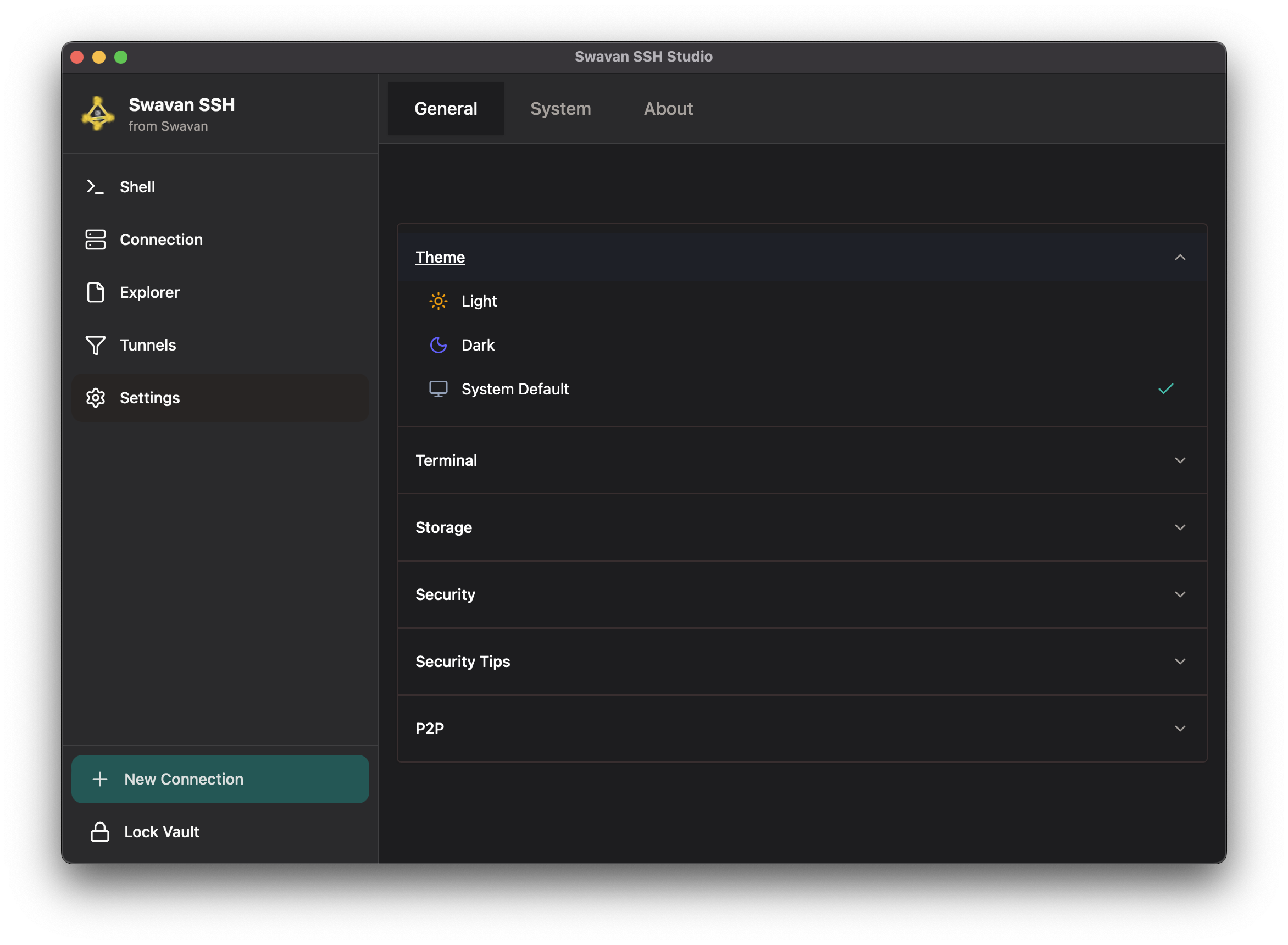
After unlocking you will see the full application. The sidebar gives access to all features.
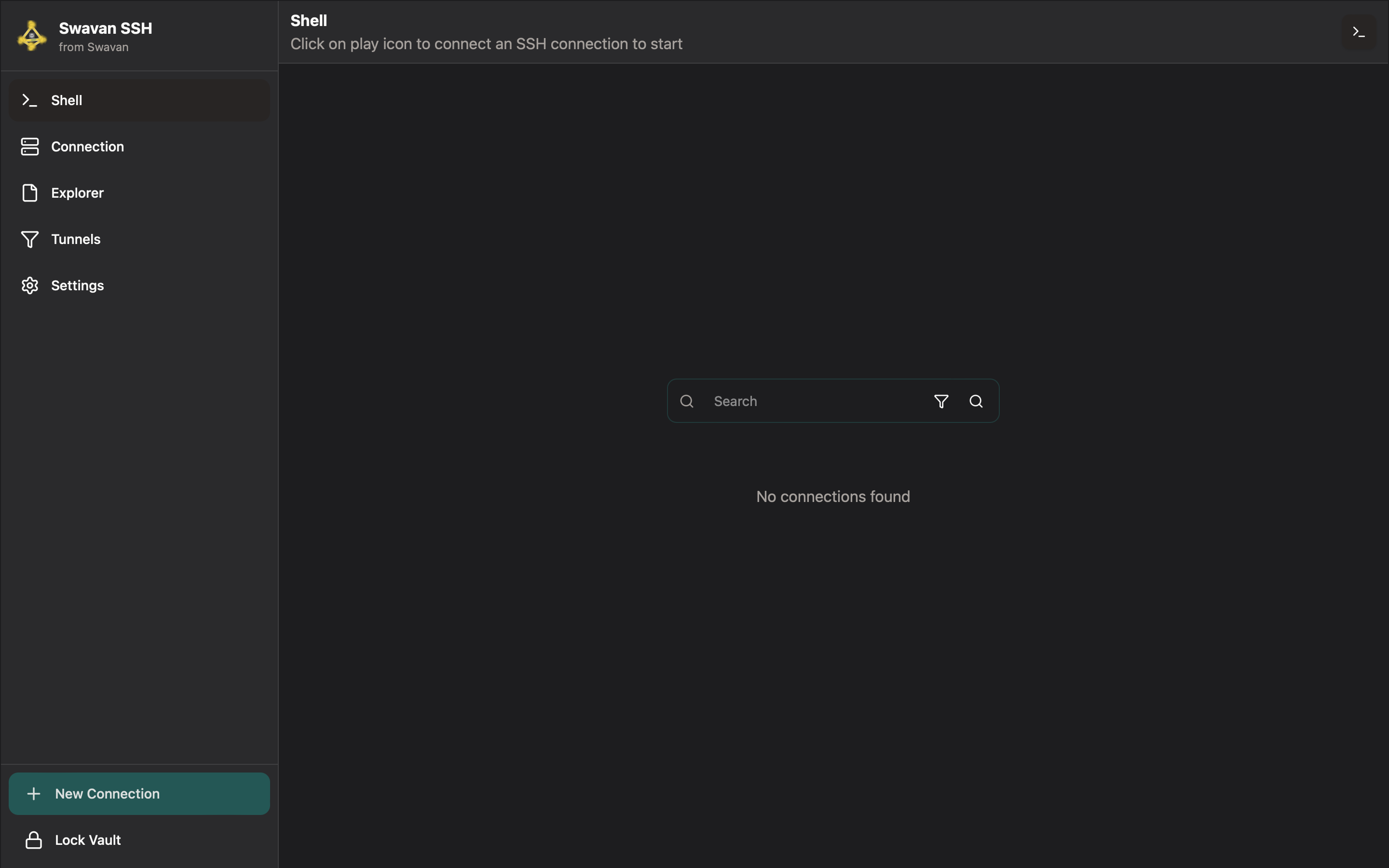
- Terminal icon — multi-tab SSH terminal sessions
- Connections icon — manage saved SSH connections
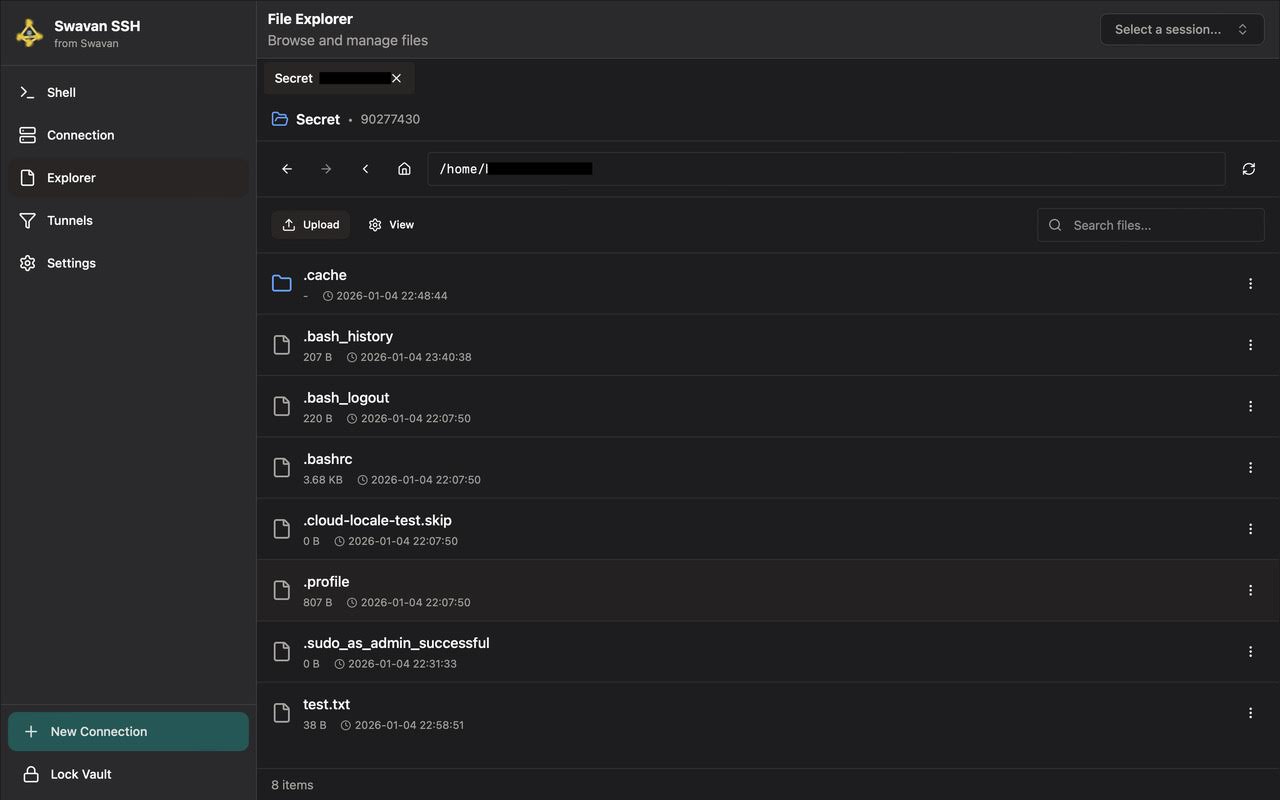
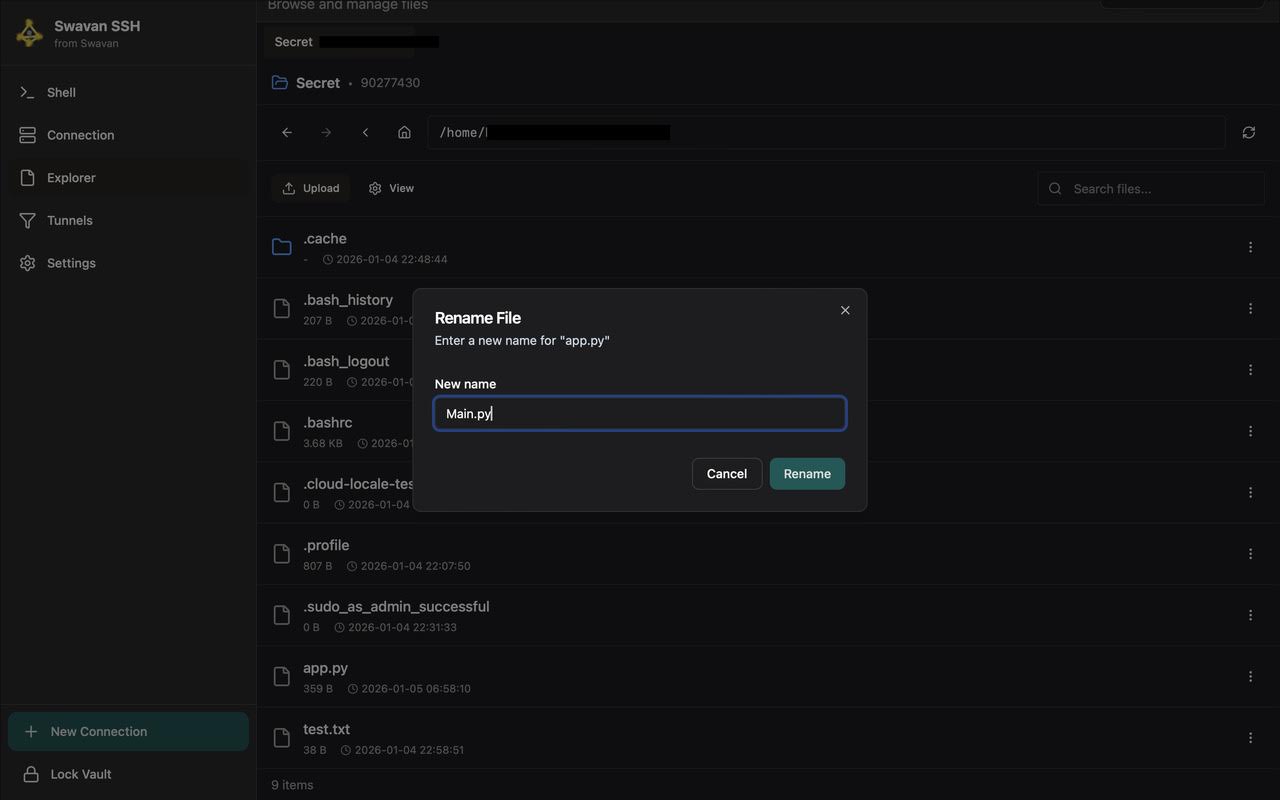
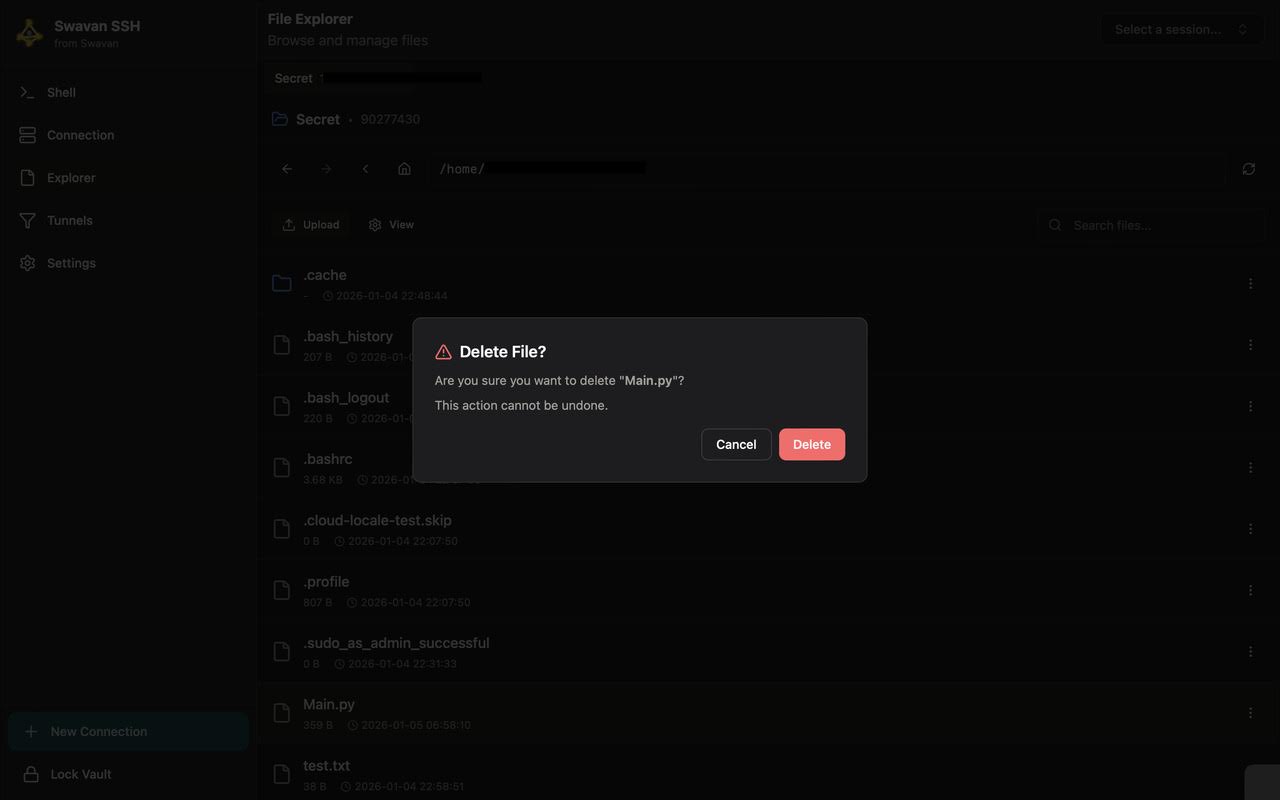
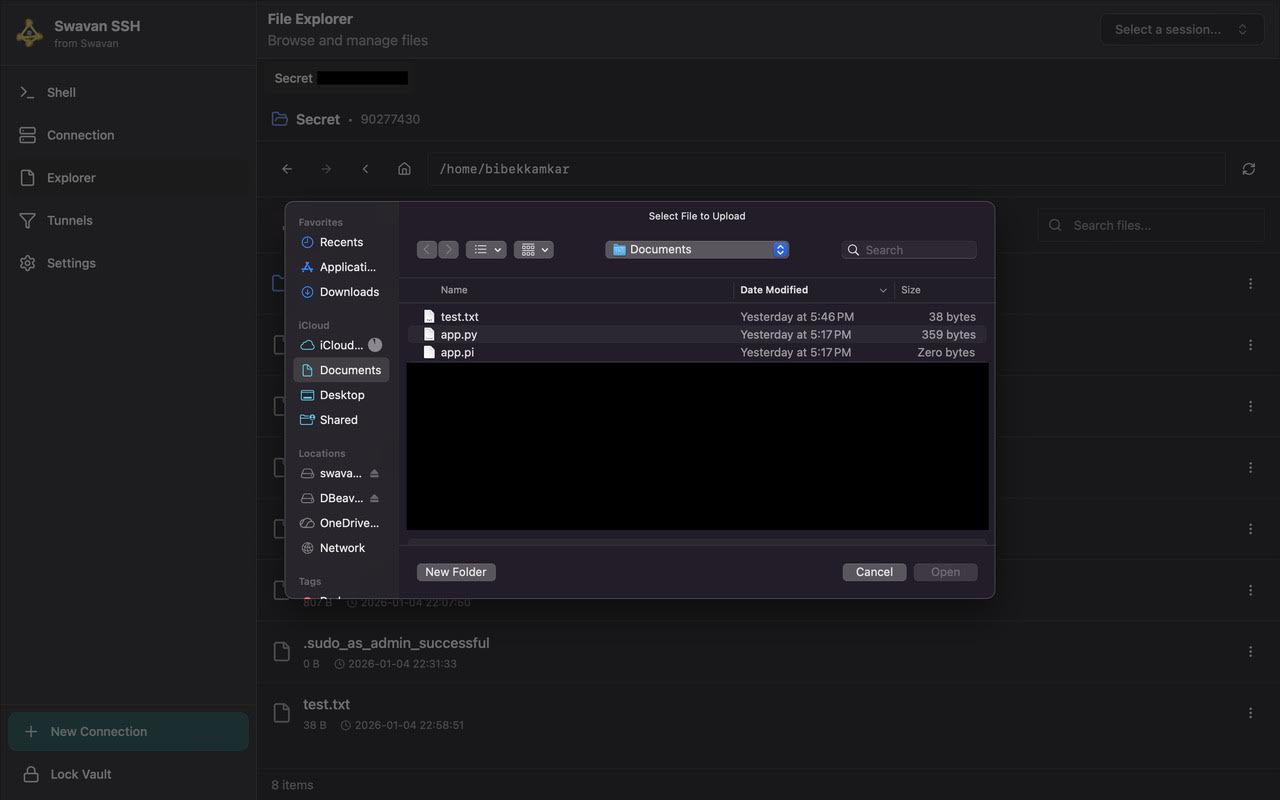
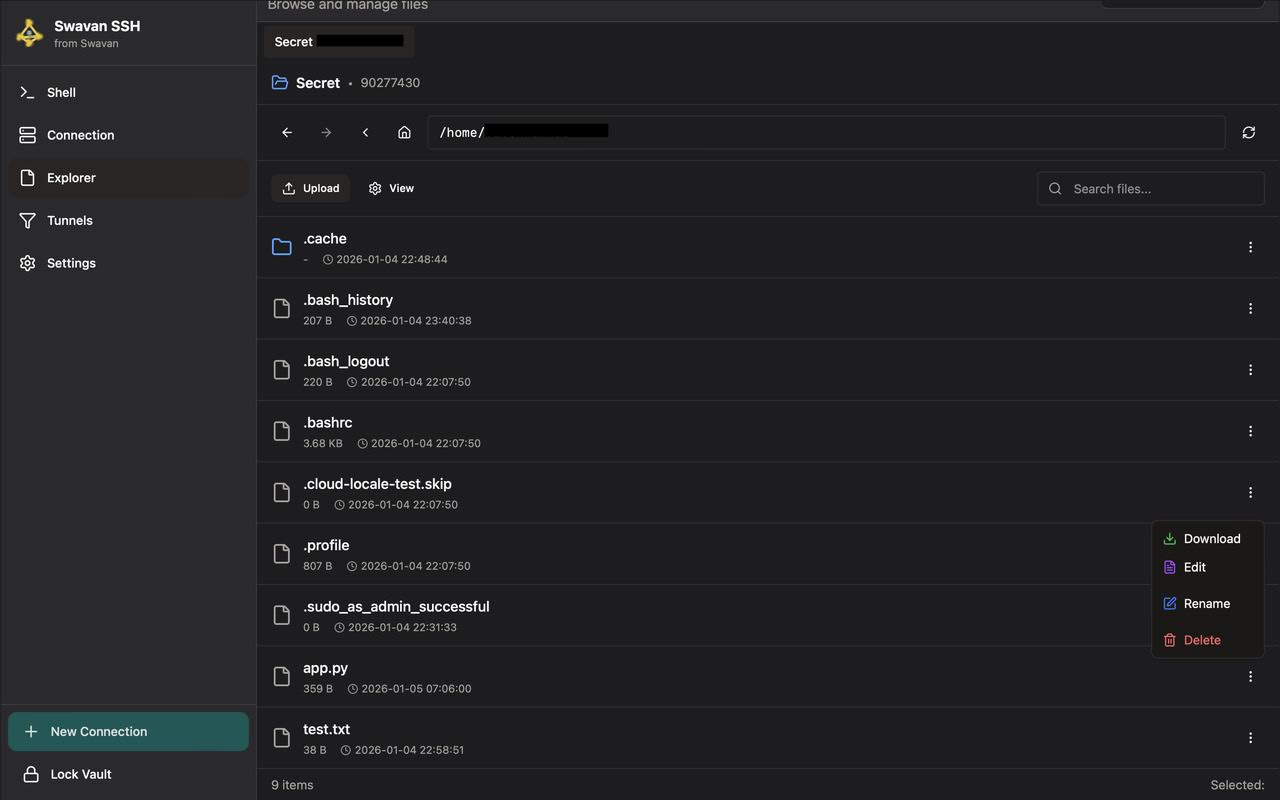
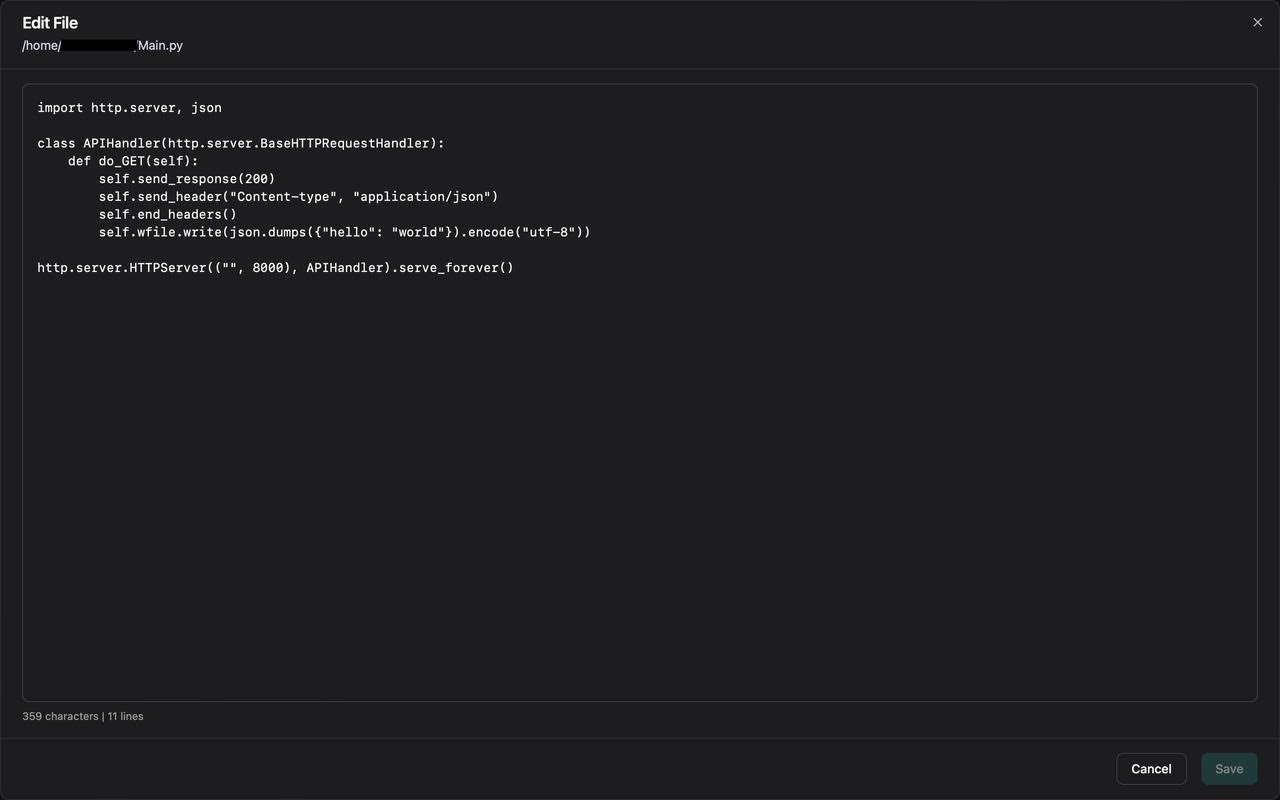
- Explorer icon — remote file browser and editor
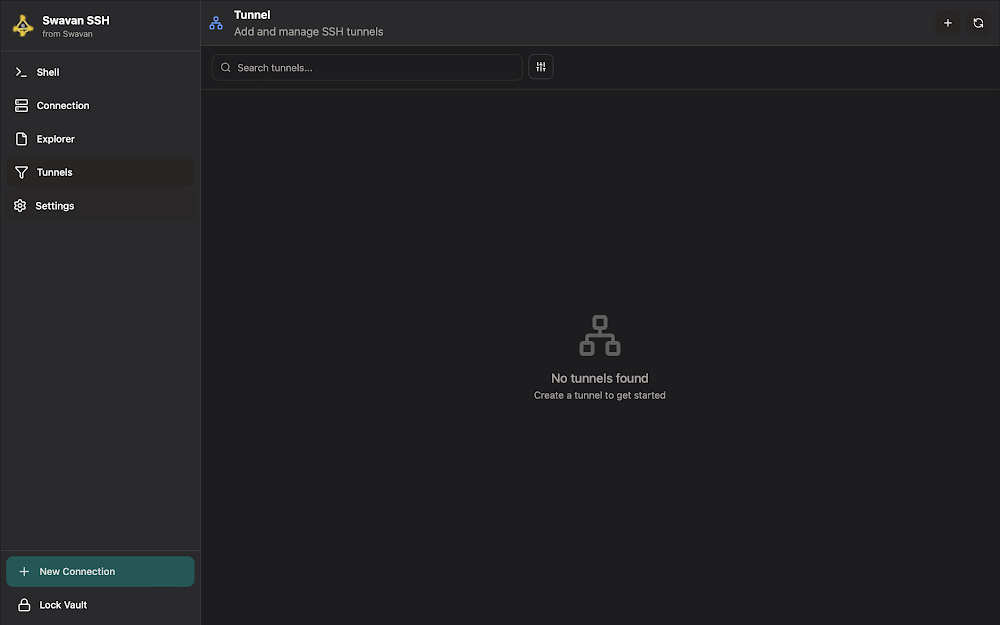
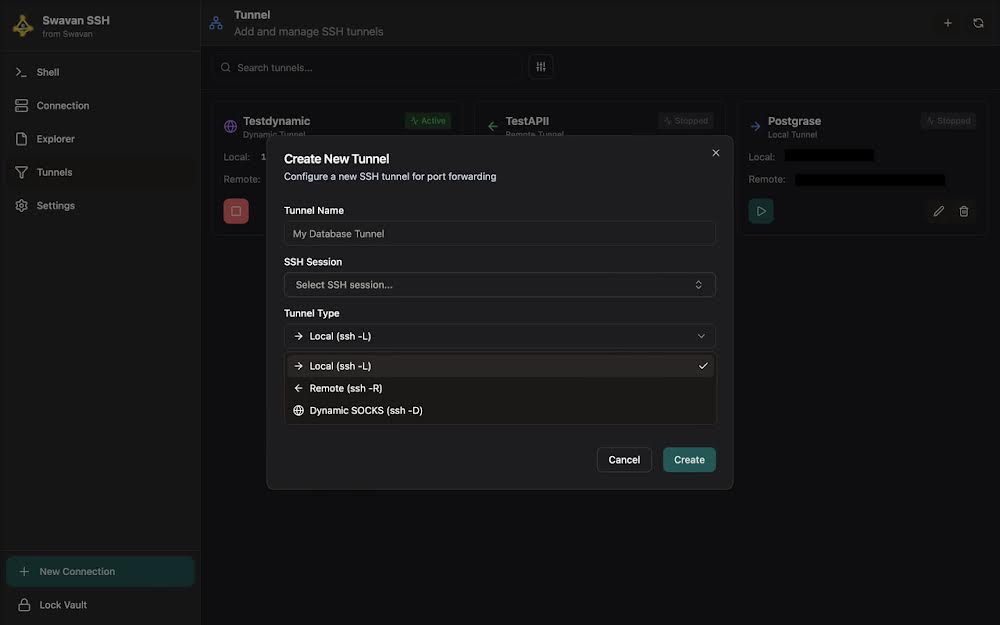
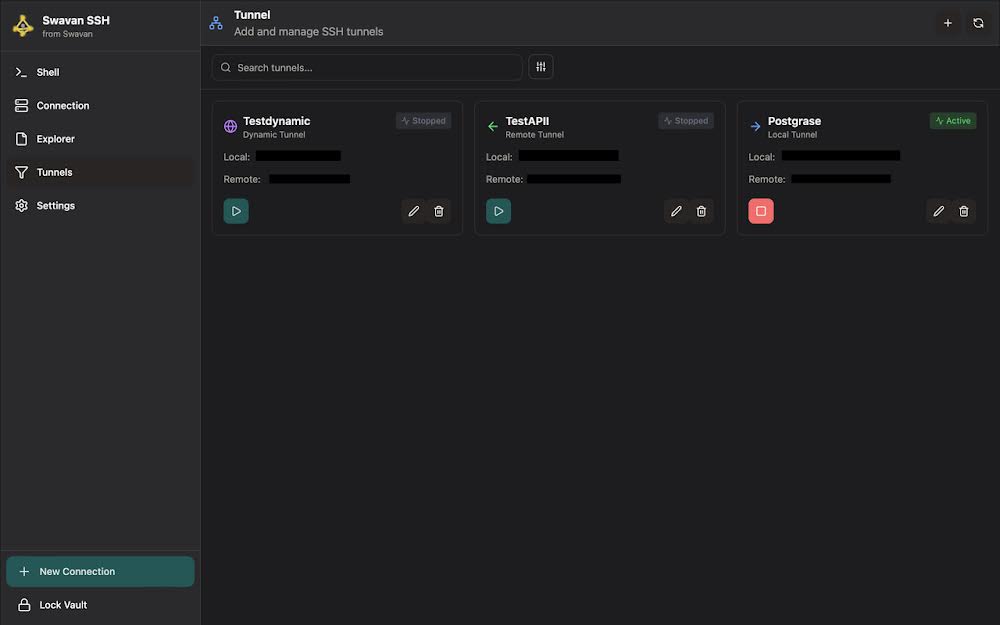
- Tunnels icon — SSH port forwarding and SOCKS proxy
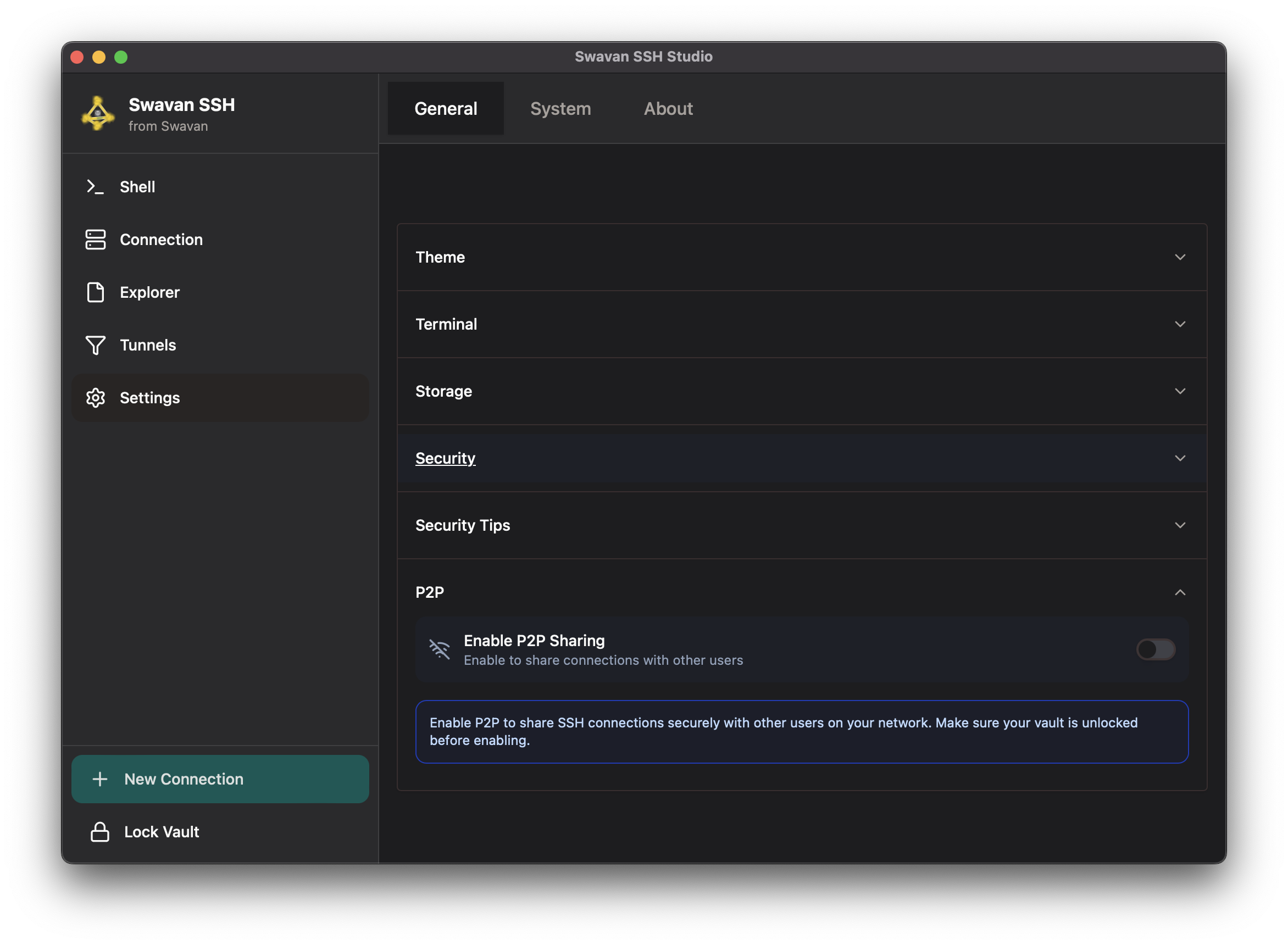
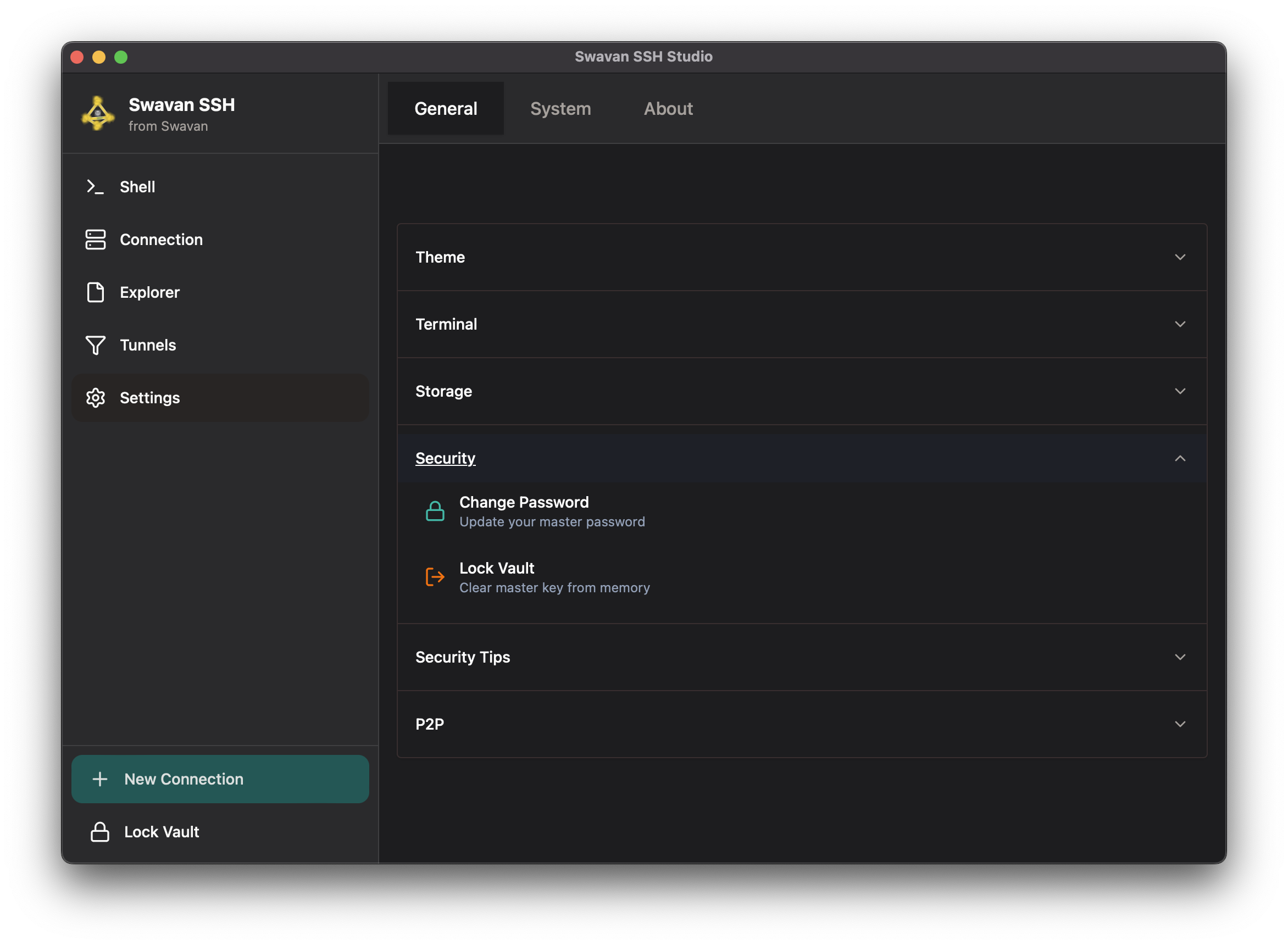
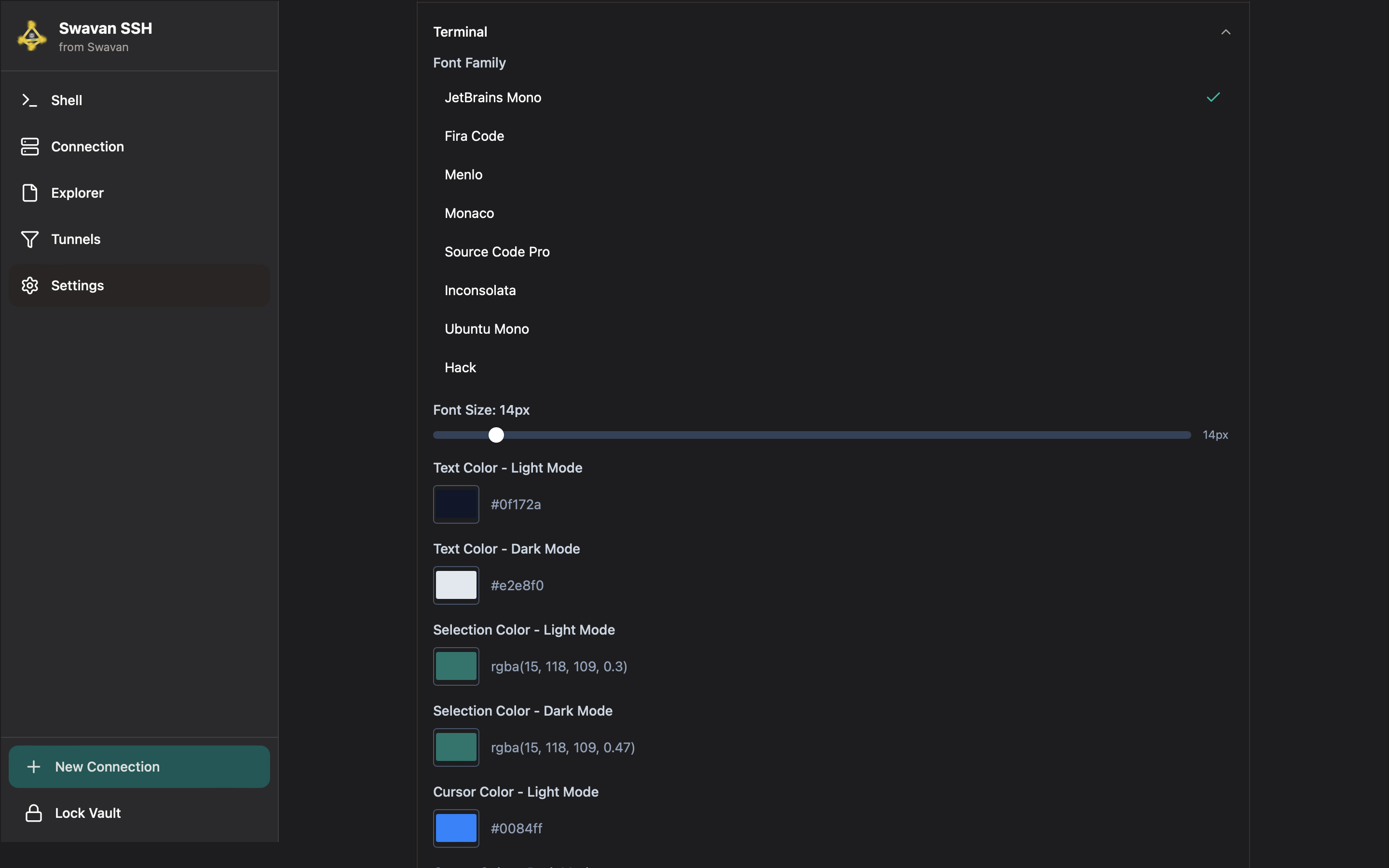
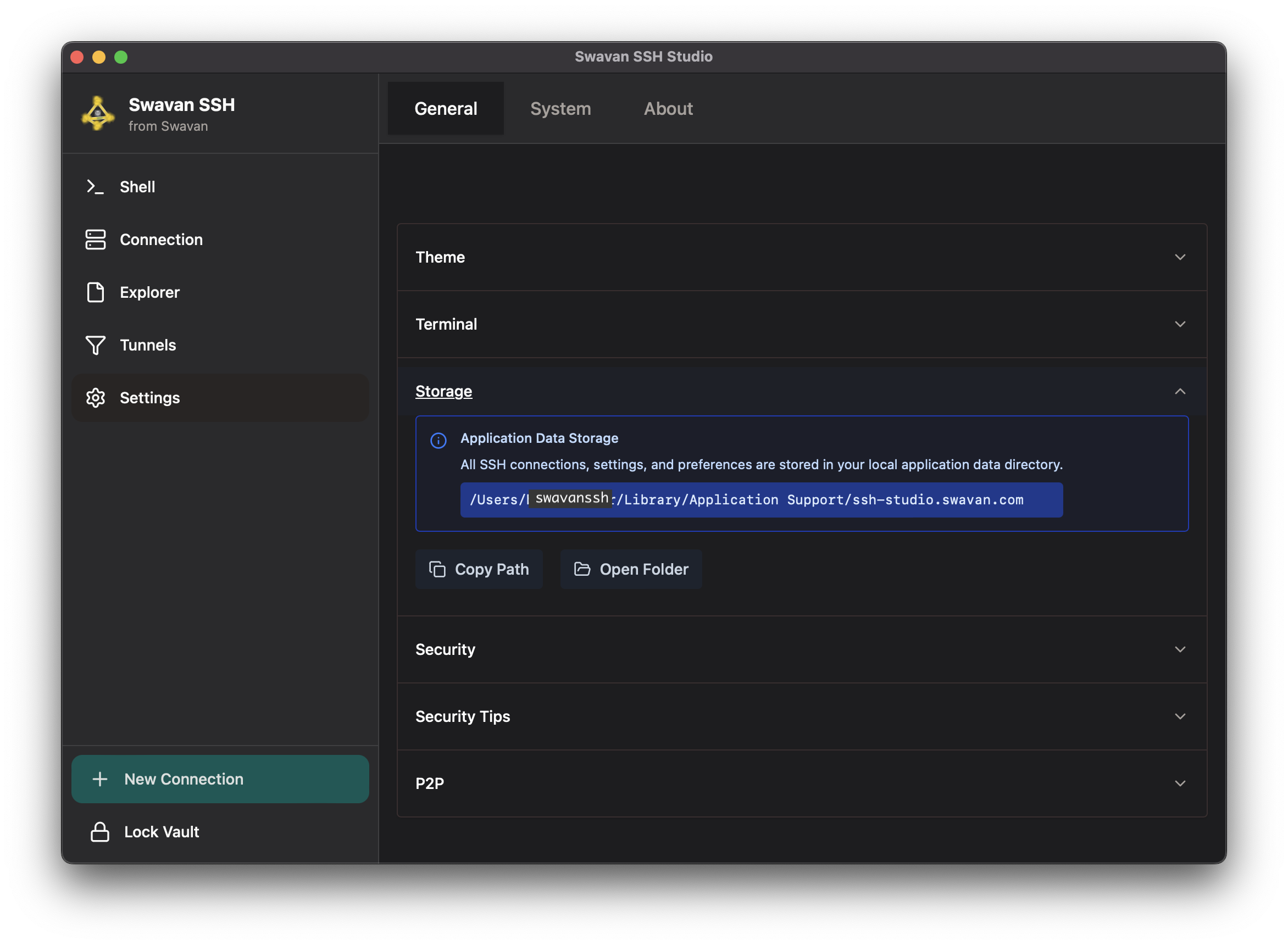
- Settings icon — preferences, security, customization